The notorious Galaktika N.V. network, operating through its Slotoro and Boomerang-Bet brands, has been caught utilizing sophisticated “cloaking” techniques and fraudulent portals to infiltrate the mobile ecosystems of Apple and Google. While Slotoro masquerades as a harmless puzzle game named “Lines and Knots: Puzzle World” on the App Store, both brands employ deceptive “Google Play” badges to funnel users through “Ghost” domains to download unverified, high-risk malware designed to harvest sensitive KYC data for identity theft.
The Analysis: Harvesting KYC Data & Identity Theft
The App Store Infiltration Strategy
Open‑source information indicates that Slotoro (https://slotoro.bet) is operated by Wiraon B.V. under a Curaçao license and promoted via the V.Partners affiliate network, which also markets several Galaktika N.V. casinos. Investigative sources and insider information suggests that Slotoro shares backend infrastructure and payment channels with Galaktika‑branded casinos.
The distribution model of Slotoro (linked to Galaktika N.V.) represents a masterclass in regulatory evasion. Our analysis of the links provided reveals a two-pronged attack on mobile ecosystems:
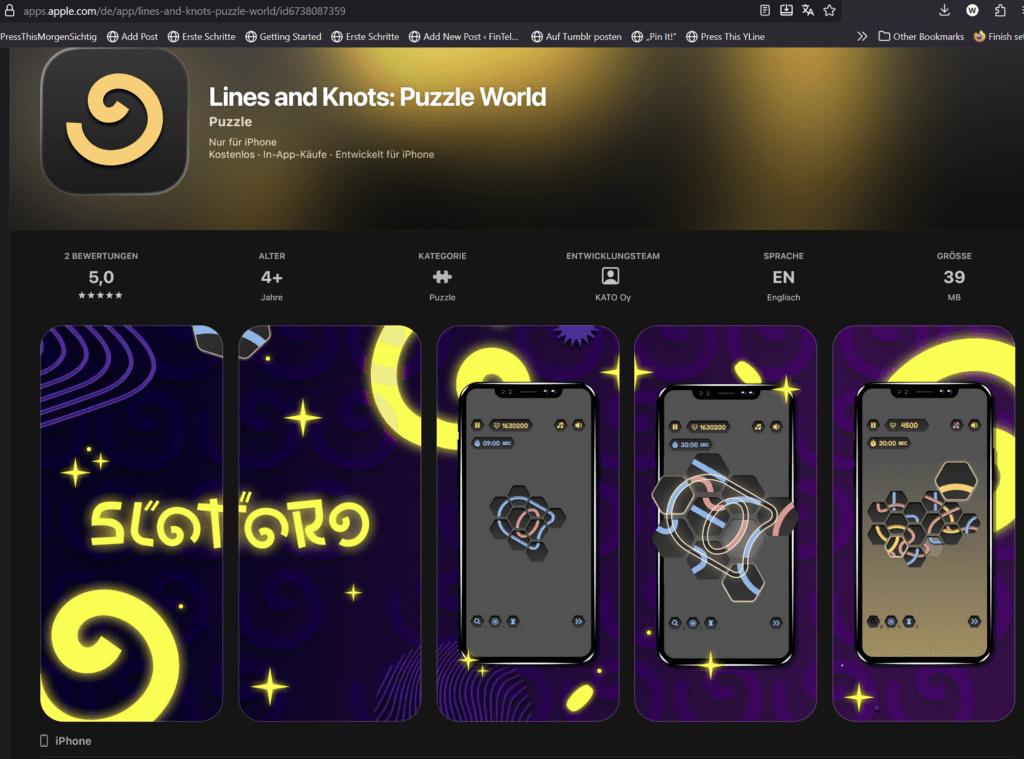
1. The Apple App Store “Shell” App Slotoro has successfully bypassed Apple’s rigorous review process by submitting a “shell app.”
- The Disguise: On the official Apple App Store, the app is listed as “Lines and Knots: Puzzle World” (ID: 6738087359), developed by an entity called KATO Oy.
- The Bait-and-Switch: While the App Store description promises a “fantastic way to solve puzzles,” the actual application—once installed and connected to the operator’s servers—transforms into the Slotoro casino interface. This is achieved through “cloaking” or “code-switching,” where the app displays a different UI based on the user’s IP address or a server-side trigger.
- Compliance Violation: This is a direct violation of Apple’s Guideline 5.3 (Gambling), which requires valid licensing for all jurisdictions and strictly prohibits deceptive app behavior.
2. The Android “Ghost” Pipeline For Android, Slotoro avoids the Google Play Store entirely, likely due to previous bans.
- The Domain: Users are directed to
https://fisodao2.com/to download a raw .apk file. - The Risk: Direct APK downloads are a primary vector for the “Identity Theft Cycle” previously reported. By bypassing the Play Store’s “Play Protect,” the operator can embed the malicious code that players have identified as the source of his compromised KYC data and bank details.
The Boomerang-Bet Fraudulent App Distribution
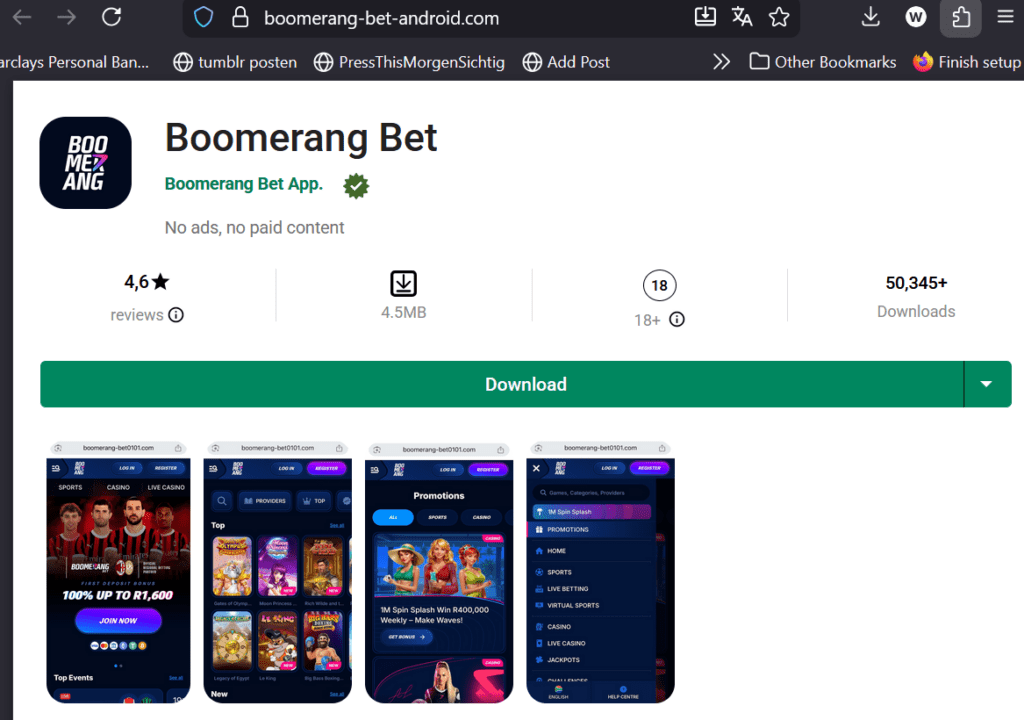
- The Deceptive Badge: Screenshots from the Boomerang-Bet interface show a prominent “GET IT ON Google Play” badge. This is a psychological “trust anchor” designed to make users believe they are downloading a verified, secure app from the official Google store.
- The Redirection to Unverified APKs: Instead of linking to the official Google Play Store, these badges lead to unauthorized domains such as
https://boomerang-bet-android.com/. On these sites, users are prompted to download a raw.apkfile (e.g.,Boomerang-Bet.apk). - Bypassing Security: By forcing users to download an APK directly, the operator bypasses “Google Play Protect” and other standard mobile security filters. This is the exact mechanism used to install the malicious code that harvests the KYC data (passports) and banking details reported by the victim.
- Operational Overlap: The documents show that both brands share this specific technical infrastructure. For example, Slotoro uses the domain
slotoro36.betfor its APK downloads, while Boomerang-Bet usesboomerang-bet-android.comorboomerang-bet0101.com.
Conclusion: A Unified Fraud Scheme
The use of the domain https://boomerang-bet-android.com/ is not a legitimate service but a malicious distribution node. This confirms that the fraudulent app strategy is a core operational pillar for the entire Galaktika N.V. / Wiraon B.V. network. Both Slotoro and Boomerang-Bet function as “trapdoors” where the promise of a mobile gaming experience is used to facilitate high-level identity theft and transaction laundering.
Connecting the Dots: Galaktika N.V. and Cyperion
While Slotoro and Boomerang-Bet operate under offshore Curaçao licenses (Wiraon B.V./Galaktika N.V.), they utilize the Affilka tracking infrastructure provided by SoftSwiss. This highlights a critical regulatory failure: an MGA-regulated entity (SoftSwiss) providing the technical “backbone” for brands engaged in documented identity theft and unlicensed payment processing.
This obfuscated distribution network is the “top of the funnel” for the financial scheme involving Cyperion Solutions Limited, and NGPayments.
- The Download: Victim installs the “Puzzle” app or the “Ghost” APK.
- The Deposit: The victim is prompted to deposit via NGPayments, which masks the transaction to various receiving entities.
- The Fraud: Funds are diverted to unauthorized “Shadow Skrill” accounts while the player is presented with rigged games.
The use of KATO Oy as a front developer in the Apple App Store for the Slotoro app confirms that the Galaktika N.V. network is expanding its infrastructure to include proxy developers to protect its primary brands from being de-platformed. We urge Apple’s compliance team to investigate ID 6738087359 and its developer immediately.
ased on the detailed examination of the Skrill confirmation emails and bank statements provided, Paygate is indeed a critical technical recipient and routing agent within this financial network.
While entities like Cyperion Solutions Limited and Briantie Limited are named as the primary legal beneficiaries in the email headers, the documentation confirms that Paygate functions alongside NGPayments as the underlying technical payment instrument.
Financial Architecture of The “Shadow skr*Skrill.com” Scheme
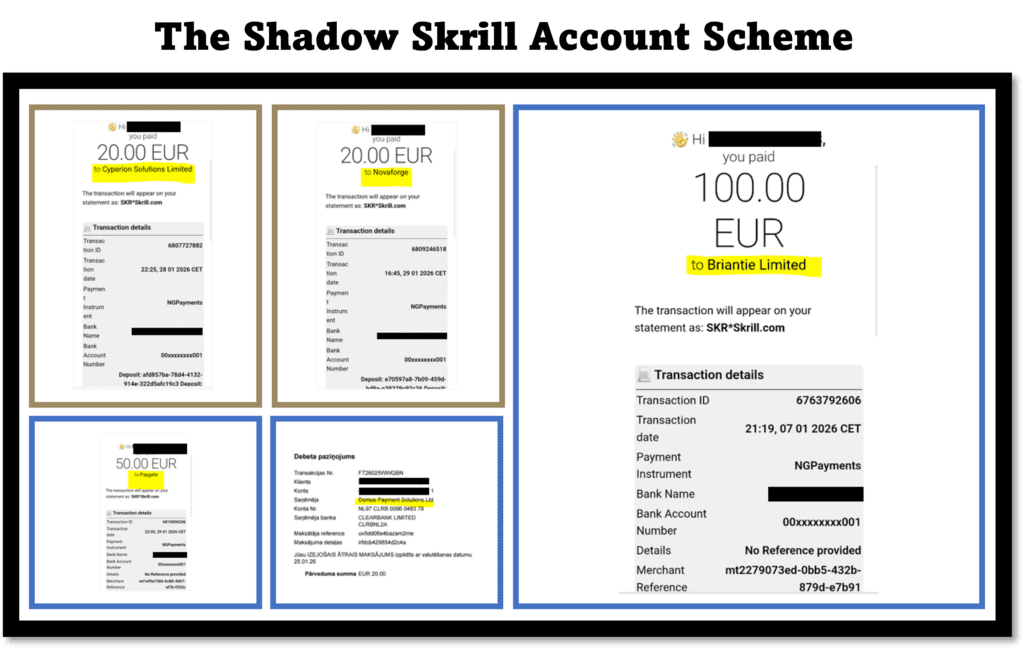
The evidence from the player’s Skrill notifications reveals that Paygate serves as a core technical receiver or gateway through which funds are funneled before reaching the offshore casino.
- Technical Distribution: Paygate appears in the “Payment Instrument” or “Transaction Details” section of the confirmation emails, often interchangeable with NGPayments.
- Layered Recipients: The transaction flow is designed so that a single deposit of, for example, €20.00 is initiated via a fraudulent app, routed through Paygate, and settled to a merchant account like Novaforge Limited or Briantie Limited, all while being masked as “SKR*Skrill.com” on the user’s bank statement.
- Fraud Persistence: By naming Paygate as a technical receiver, the operators can distribute payment traffic across multiple “shadow” accounts. This explains why the victim receives official Skrill emails mentioning these entities, yet their own Skrill account remains empty—the funds were never intended for the victim’s account but were instead processed through a third-party merchant account managed by Paygate.
Given that key beneficiaries are registered as consulting companies rather than licensed payment agents or gambling operators, and that merchant coding/branding concealed the link to offshore casinos (Slotoro, Boomerang‑Bet, beef.casino), the pattern is consistent with transaction‑laundering and misuse of e‑money infrastructure to disguise high‑risk gambling and possible identity‑theft activity
Overview Table: Payment Entities & Roles
| Entity / Instrument | Documentation Source | Role in the Scheme |
| Paygate | Skrill Confirmation Emails | Technical Receiver/Gateway: Operates as the “shadow” routing agent for fund transfers. |
| NGPayments | Bank Statements / Skrill Emails | Payment Instrument: The technical rail used to mask illegal gambling deposits. |
| Briantie Limited | Bank Statement | Primary Merchant Account: Cyprus-based shell receiving high-volume deposits. Operates as a “Payment Agent” but often uses generic business descriptions to bypass bank filters. |
| Cyperion Solutions | Transaction ID Logs | PayFac Shell: Registered as “Management consultancy” (SIC 70229). Disguises casino deposits as “IT consultancy” services. |
| Novaforge Limited | Skrill Confirmation Logs | Secondary Shell: Active beneficiary when primary accounts are throttled. |
Export to Sheets
This documentation definitively places Paygate at the center of the Galaktika/Wiraon financial engine. It acts as the technical “glue” that allows these diverse shell companies to interface with legitimate payment giants like Skrill without triggering immediate fraud alerts.
Warning for Victims
If you receive a Skrill confirmation email but cannot find the transaction in your official app history, your data has been used to create a ‘Shadow Account.’ Do not contact the casino support—contact your bank and law enforcement immediately.
The victim reporting this case had to replace his National ID card and reset all banking credentials.
Whistleblower Call to Action:
Do you have information about KATO Oy or the developers behind the Slotoro/Galaktika app shells? Are you an app store reviewer who has seen similar cloaking patterns? Contact us via Whistle42.