RagazzeInVendita (RIV) presents itself as an Italian-facing adult cam/chat platform, but its own terms route payment services through Pagorapido SA in Las Palmas, with card statements said to show Pagorapido. Pagorapido’s own site, in turn, markets payment processing for ecommerce, marketplaces, and online content and states that it is “Property of Hydra Group.” FinTelegram conducted a comparative analysis of RIV’s payment rails against those of XLoveCam and CrushOn.ai.
Key findings
- RIV does not present its card rail under its own name. Its terms identify Pagorapido SA as the payment-services provider and say the card statement will show Pagorapido SA.
- Pagorapido looks like a front layer, not a transparent PSP disclosure page. The site reads like generic marketing copy, not like a clearly disclosed regulated payment institution.
process1.payments.siteis not just a generic checkout page. The source code shows a full hosted-payment environment with direct card-data capture, live session logic, and merchant configuration.- Source-code analysis shows that
process1.payments.siteseems to be connected to the Cyprus EMI Payabl. - The adult payment setup is multi-layered across several rails. Card payments run through intermediary brands and shadow domains, while SEPA, PayPal, and crypto rails add further routing layers.
- RIV and XLoveCam appear to use YowPay for SEPA transfers. The reviewed bank-transfer instructions point to a Banking Circle Germany account, with different listed recipients depending on the platform.
- RIV’s PayPal rail adds another intermediary layer. The reviewed flow points to Epoch /
join.wnu.com, while XLoveCam appears to use a more direct PayPal setup. - Crypto rails were identified for RIV and XLoveCam. At XLoveCam, the reviewed flow runs through
secure.acwebconnecting.comand CoinPayments. - The compliance problem is the opacity of the payment chain. Platform brand, payment-facing brand, gateway domain, and underlying processor are split across different layers, raising obvious questions around KYB, MCC assignment, descriptor clarity, monitoring, and processor disclosure.
- This pattern fits a broader high-risk payments playbook. The more layers inserted between the merchant and the actual processor, the harder it becomes for consumers, counterparties, and supervisors to see who is really handling the transaction.
Compliance analysis
1. The disclosed RIV rail and the observed rail do not fully match
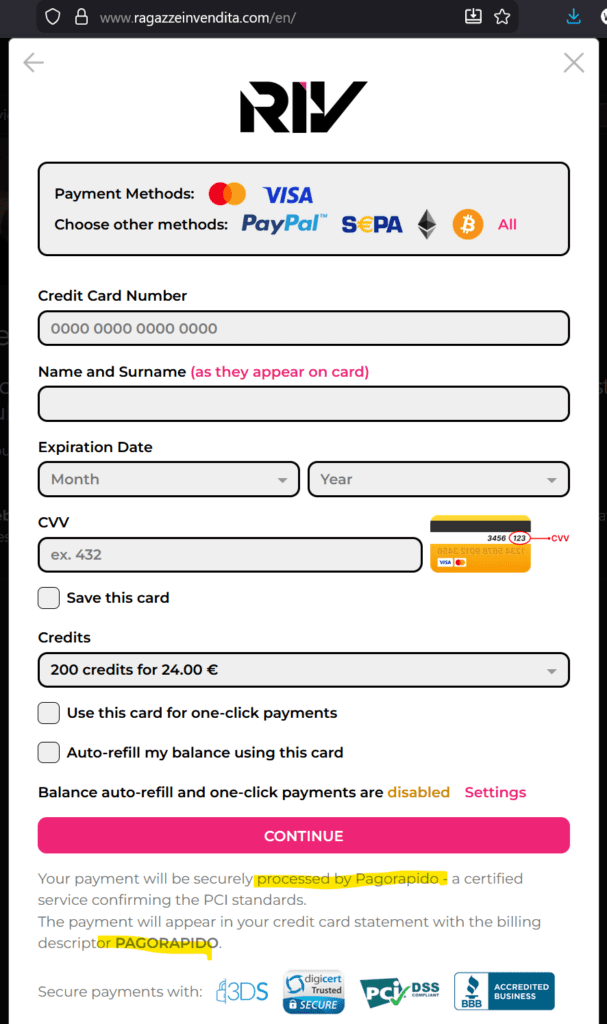
RIV’s terms are explicit: payment services are provided by Pagorapido SA, and Pagorapido SA is also the card-statement descriptor. That means RIV itself is telling users there is a separate payment layer between the adult platform and the actual card-processing stack. In FinTelegram’s reviewed checkout materials, the live card page was not served from a transparent Pagorapido domain, but from process1.payments.site. That gap matters.
In compliance terms, the key question is no longer only “who is the merchant?” but also “which entity is the contractual merchant-of-record, which entity provides the gateway, and which regulated institution is actually underwriting or routing the transaction?”
2. Pagorapido looks more like a façade layer than a transparent PSP
Independent review does not show Pagorapido presenting itself like a normal regulated European payment institution. Its site contains generic marketing copy, a single visible contact email, broad claims about serving ecommerce, marketplaces, and online-content sellers, and the footer statement “Property of Hydra Group.”
We did not find visible licensing disclosures on the site content reviewed. At the same time, the Spanish company record linked to the same address and CIF named in RIV’s terms shows a general intermediation company profile, not a clearly disclosed PI/EMI profile, and flags registry problems in 2023. That does not by itself prove illegality, but it materially weakens any claim that Pagorapido is a transparent, stand-alone, clearly regulated card processor.
3. process1.payments.site appears to be the real gateway layer
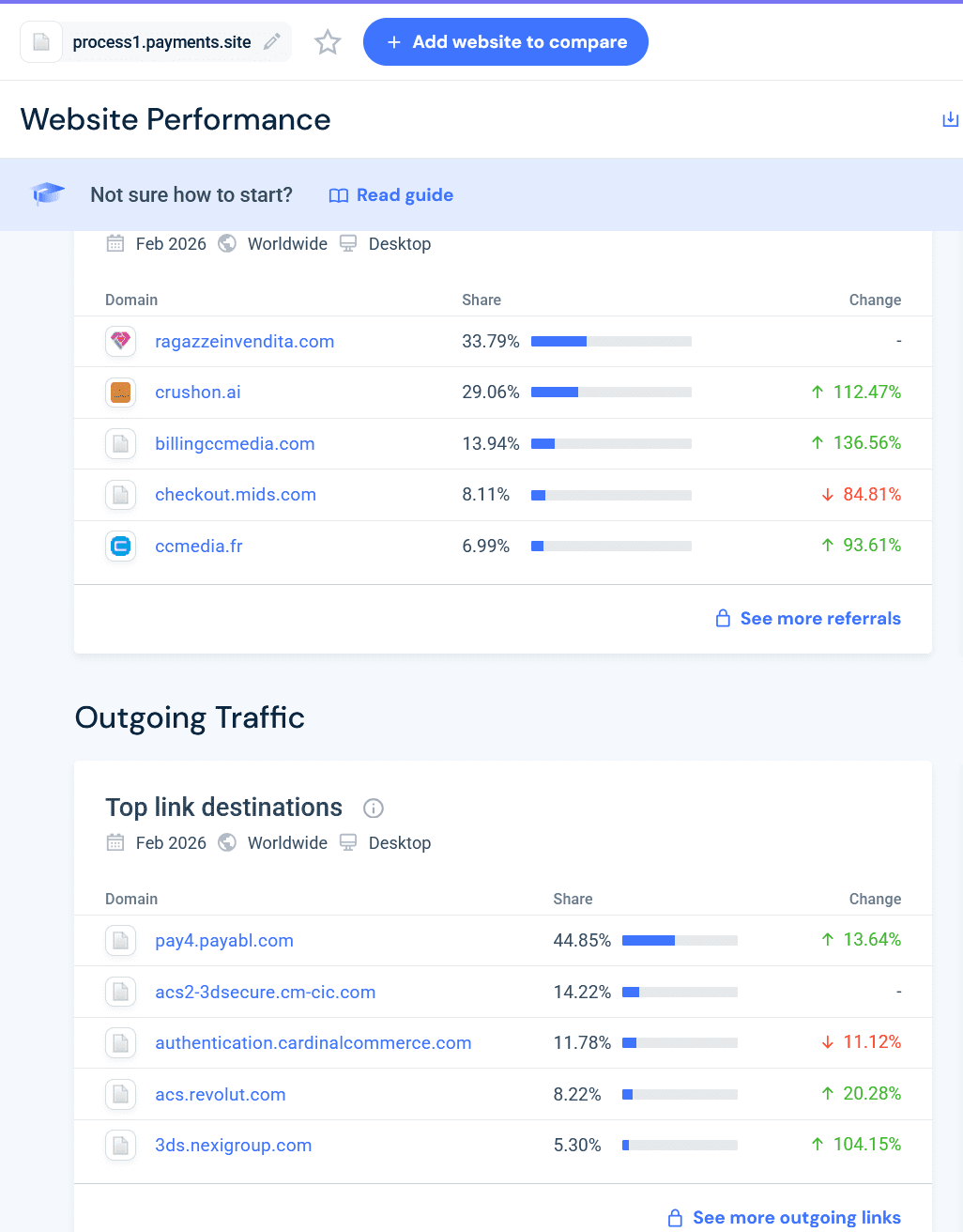
The public web fetch of process1.payments.site yields no meaningful corporate disclosure, which is itself notable for a payment touchpoint. FinTelegram’s reviewed materials show two converging facts: traffic flowing from process1.payments.site toward pay4.payabl.com, and a separate adult-adjacent checkout (crushon.ai) loading an iframe from pay4.payabl.com. Taken together, those facts support a strong conclusion that process1.payments.site is not an isolated gateway, but part of a closely tied backend card-processing ecosystem.
4. Payment Gateway Process1 hosted by Payabl
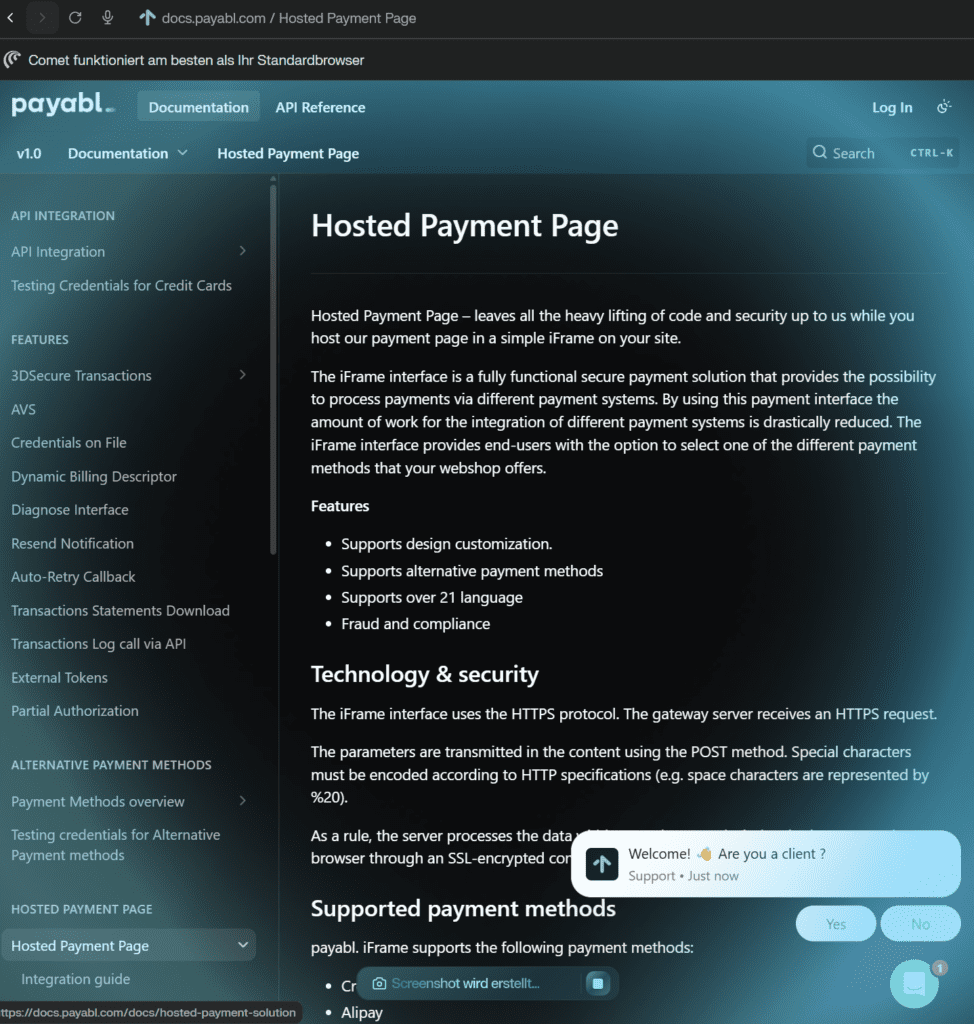
FinTelegram commissioned an expert opinion of the high-risk payment gatewayprocess1.payments.site. The forensic analysis indicates that the domain is not an independent generic checkout page but a Payabl-associated hosted payment environment operating under an opaque, non-Payabl-branded domain. The source code shows a direct technical match with Payabl’s HPP architecture, including the /hpp/ routing structure, asset paths, POST endpoints, hidden-field schema, multilingual session flow, and even Payabl branding residue in the favicon, while the live payment session identifies Cyprus-registered TECHIEPIE LTD as the merchant presented to the payer. TECHIEPIE LTD is the legal entity behind the AI-powered adult platform CrushOn.ai (see below).
In practical terms, the gateway appears to function as a shadow payment layer that collects card data on behalf of front-end merchants while obscuring the underlying payment-processing relationship from consumers, raising obvious compliance questions around merchant transparency, processor disclosure, and the use of non-branded infrastructure in higher-risk payment flows.
Download the Intelligence report for the Payment Gateway
5. Cross-platform recurrence increases the compliance concern
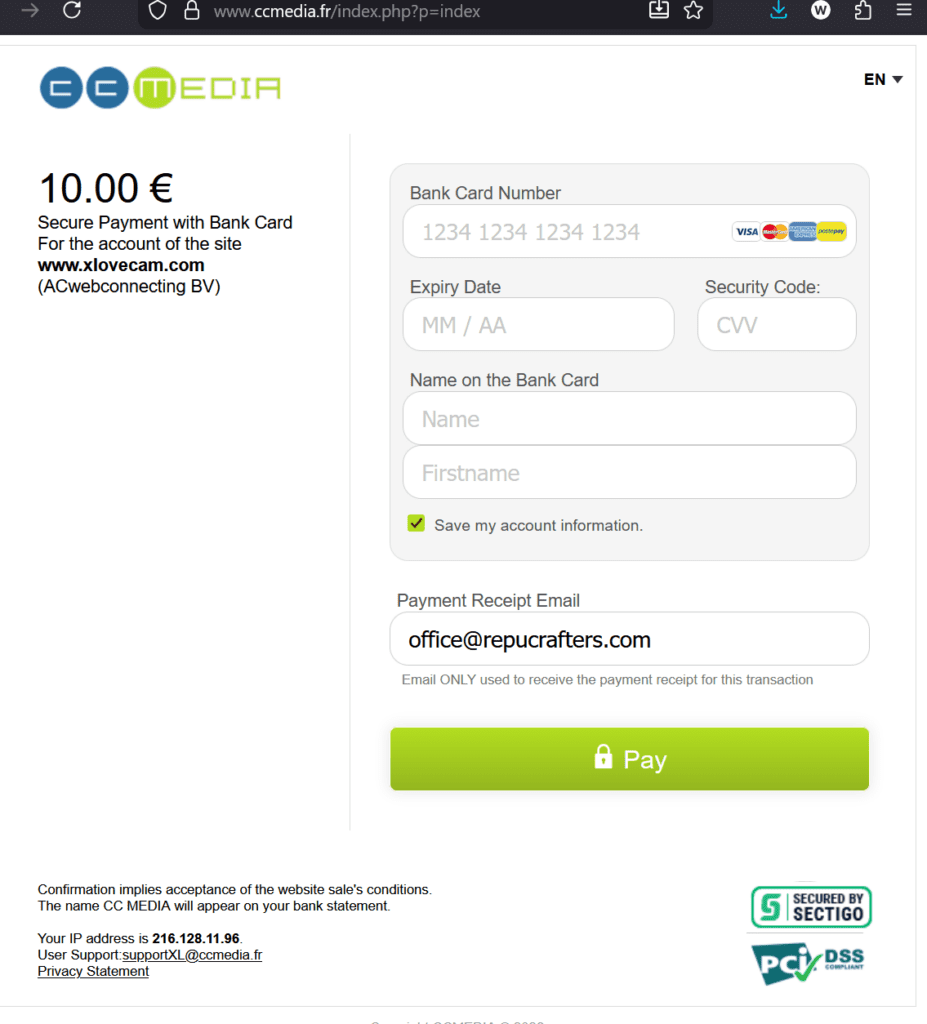
The RIV pattern is not isolated in the materials reviewed for this report. FinTelegram’s screenshots show the same process1.payments.site layer appearing in the card rail of xlovecam.com, where the visible intermediary is CCMedia, and in the NSFW AI platform CrushOn.ai, where the iframe described above was separately observed. Independent research confirms that billingccmedia.com redirects to ccmedia.fr; ccmedia.fr identifies CCMedia as a Marseille SARL and advertises “secure internet micropayments.”
Independent research also confirms that AC Webconnecting’s terms describe an adult-platform family including XLove, XLovecam, XXXLove, and XLovegay, with users redirected through various domains and white labels. crushon.ai itself identifies TECHIEPIE LTD in Nicosia in its site footer. This reuse of one gateway family across multiple adult or adult-adjacent merchants is a classic signal that risk should be assessed at network level, not merchant by merchant.
6. Why the layering is a compliance problem
The EBA’s own work on payment institutions is directly relevant. Supervisors told the EBA that payment institutions often have a higher proportion of higher-risk customers; that platforms and marketplaces create additional layers which increase ML/TF risk; that cross-border business is a major risk factor; that new technology and remote onboarding raise risk; and that widespread use of intermediaries is one of the most significant delivery-channel risks in the PI sector.
Applied here, the concern is straightforward: a consumer sees an adult brand, the statement may show a different descriptor, the visible payment brand may itself be opaque, and the underlying gateway may sit inside a different regulated processor’s environment. That can undermine clean KYB, merchant-descriptor accuracy, MCC integrity, chargeback analysis, suspicious-activity escalation, and effective screening of restricted or sensitive merchant categories.
Payment Rails Overview
SEPA / Bank Transfer
- RagazzeInVendita (RIV) and XLoveCam appear to use YowPay (
yowpay.com) for SEPA deposits. - Reviewed payment instructions show transfers routed to a YowPay account at Banking Circle Germany under IBAN
DE39 2022 0800 0059 2403 75. - The listed recipients differ by platform: Hydro Group for RIV and AC Webconnecting for XLoveCam.
- No comparable SEPA / bank-transfer rail was identified for CrushOn.ai in the reviewed materials.
PayPal
- All three platforms reviewed appear to offer a PayPal-based fiat deposit option.
- At RIV, the PayPal flow appears to run via Epoch (
epoch.com) and the gatewayjoin.wnu.com, adding an intermediary layer between the platform and PayPal. - At XLoveCam, PayPal appears to be integrated more directly, without the additional payment-facilitator layer observed in the RIV flow.
- CrushOn.ai also appears to offer PayPal as a fiat-funding option.
Crypto
- A crypto rail was identified for RIV and XLoveCam.
- At RIV, customers appear to deposit directly into designated crypto wallets linked to the platform.
- At XLoveCam, crypto deposits appear to be routed through
secure.acwebconnecting.comand CoinPayments (coinpayments.net). - No comparable crypto rail was identified for CrushOn.ai in the reviewed materials.
Card Payments
- The card-payment rail remains the most compliance-sensitive layer in this review.
- At RIV, the visible payment-facing brand is Pagorapido, while the observed card-processing flow leads into
process1.payments.site, a Payabl-associated hosted payment environment. - At XLoveCam, the card rail appears to run through CCMedia and then into
process1.payments.site. - At CrushOn.ai, reviewed materials indicate card-payment exposure through
process1.payments.siteand a separate Payabl-linked flow viapay4.payabl.com.
Compliance Takeaway
Across the reviewed adult platforms, the payment architecture appears deliberately layered: visible platform brands sit on top of intermediary payment-facing entities, which in turn connect to underlying gateway infrastructure. This structure may serve commercial and operational purposes, but from a compliance perspective it reduces transparency around the true payment chain, complicates merchant identification, and raises obvious questions around KYB, MCC accuracy, descriptor clarity, monitoring, and processor disclosure in higher-risk merchant segments.
Summary table
| Brand / site | Disclosed entity | Jurisdiction(s) | Observed / declared rail | Compliance note |
|---|---|---|---|---|
| RagazzeInVendita (RIV) | RIV terms name Pagorapido SA, Calle San Agustin 13, Las Palmas, CIF A76360437 | Italy-facing front end; Owner: Bulgarian Hydra Group EOOD; Spain payment layer | ragazzeinvendita.com → Pagorapido SA descriptor/payment layer → observed process1.payments.site gateway | Terms disclose Pagorapido, but reviewed checkout materials indicate a different operational gateway. |
| Pagorapido | Site says “Property of Hydra Group”; Spanish company data identifies Pagorapido SA | Hydra-linked branding; Spain company record | Markets payment collection for ecommerce, marketplaces, and online content | Opaque PSP presentation; company-data record shows intermediation object and 2023 registry/NIF problems. |
| XLoveCam | AC Webconnecting terms place XLovecam within the SNV / ACW platform family; CCMedia is Marseille SARL | Curaçao / Netherlands / France | reviewed materials: xlovecam.com → ccmedia.fr / billingccmedia.com → process1.payments.site | Shows the same hidden-gateway pattern with a different visible intermediary. |
| CrushOn.AI | TECHIEPIE LTD shown in site footer | Cyprus / US (Dover address also shown in footer) | reviewed materials: crushon.ai → process1.payments.site; alternate observed rail via Payabl iframe | Adult-adjacent AI site reusing the same gateway family strengthens the network-level inference. |
Call for insiders and whistleblowers:
FinTelegram is seeking additional information from insiders at Pagorapido, Hydra-linked entities, CCMedia, AC Webconnecting, acquiring partners, scheme-monitoring teams, and compliance vendors. In particular, we are interested in merchant onboarding files, MCC assignment records, statement-descriptor policies, reserve/chargeback rules, suspicious-activity escalation protocols, and contracts governing the use of process1.payments.site and pay4.payabl.com in adult-payment flows. Please share information confidentially via Whistle42.