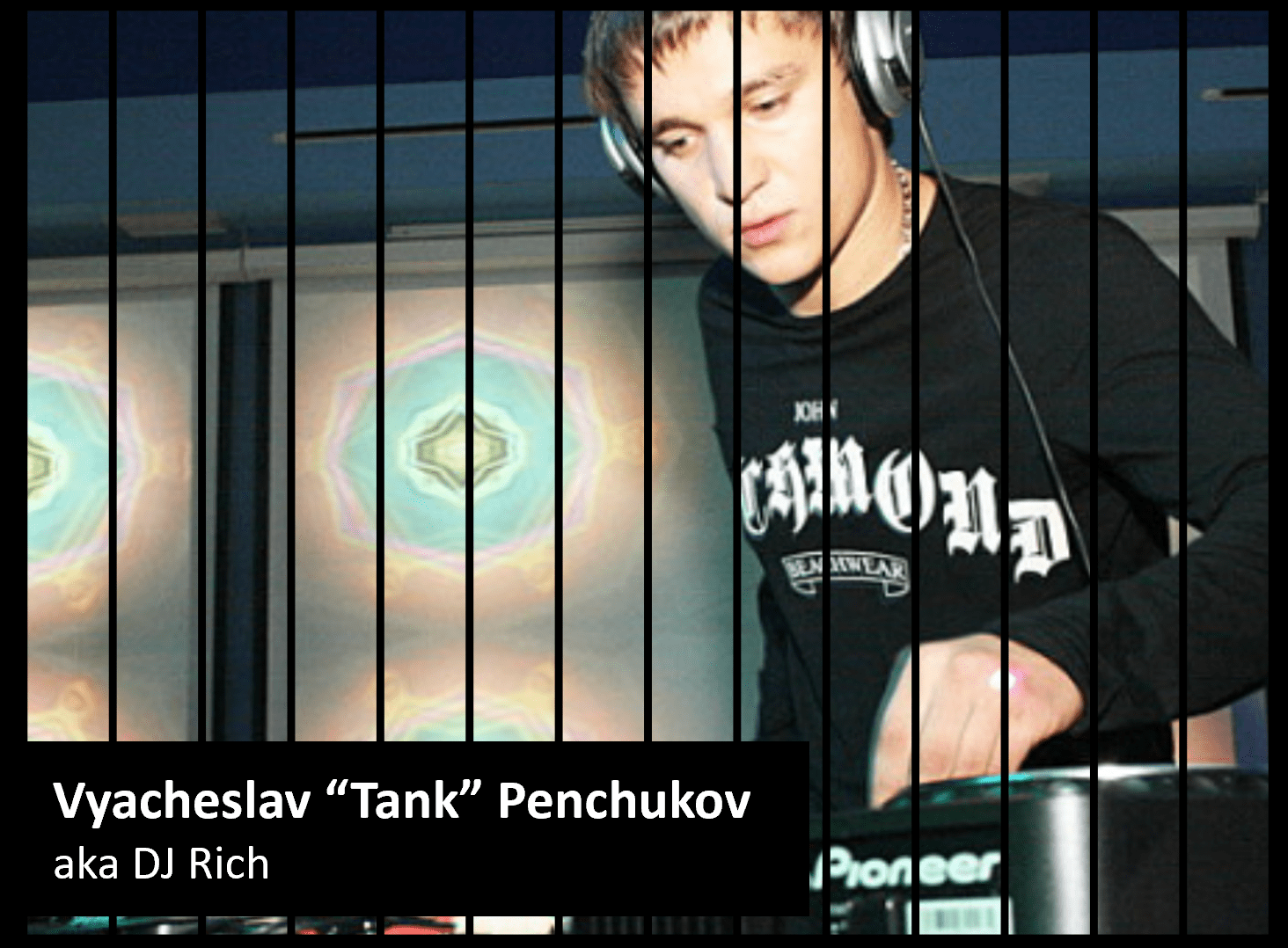
Success for international cybercrime enforcement: Vyacheslav Igorevich Penchukov, a Ukrainian national, has pleaded guilty to his involvement in two extensive malware operations that resulted in tens of millions of dollars in losses. Penchukov’s guilty plea followed his 2022 arrest in Switzerland and subsequent extradition to the United States in 2023. Penchukov was once listed among the FBI’s most wanted fugitives, evading capture for nearly a decade before his arrest.
Vyacheslav “Tank” Penchukov, 37, aka Vyacheslav Igorevich Andreev and DJ Rich, of Donetsk, faced charges related to his leadership roles in the notorious “Zeus” and IcedID malware schemes, entering guilty pleas for one count of conspiracy to commit a racketeer influenced and corrupt organizations (RICO) act offense and one count of conspiracy to commit wire fraud, respectively. Recognized for his significant part in these cybercriminal activities, Penchukov was once listed among the FBI’s most wanted fugitives, evading capture for nearly a decade before his arrest.
Scheduled for sentencing on May 9, Penchukov could face up to 20 years in prison for each count, with the final sentence to be determined by a federal judge considering the U.S. Sentencing Guidelines and other statutory factors.
Acting Assistant Attorney General Nicole M. Argentieri highlighted the severe impact of Penchukov’s actions, stating that the malware groups he led compromised thousands of computers, leading to substantial financial losses and even disrupting critical care at a major hospital due to a ransomware attack.
Court documents reveal that Penchukov played a pivotal role in a racketeering enterprise that, from May 2009 onwards, deployed the “Zeus” malware to hijack victims’ banking information, facilitating unauthorized fund transfers and resulting in significant financial damages. The criminal enterprise utilized “money mules” across the United States and beyond to funnel the stolen funds to overseas accounts controlled by Penchukov’s associates.
Penchukov was named in a 2014 indictment by the U.S. DOJ as a top figure in the JabberZeus Crew. Accoring to KrebsonSecurity, the JabberZeus malware was custom-made for the crime group by the alleged author of the Zeus trojan — Evgeniy Mikhailovich Bogachev, a top Russian cybercriminal with a $3 million bounty on his head from the FBI.
Penchukov’s political connections helped him evade prosecution by Ukrainian cybercrime investigators for many years. The late son of former Ukrainian President Victor Yanukovych, Victor Yanukovych Jr., would serve as godfather to Tank’s daughter, Miloslava. Through his connections to the Yanukovych family, Tank was able to establish contact with key insiders in the top tiers of the Ukrainian government, including law enforcement.
Penchukov resumed his criminal endeavors with the IcedID or Bokbot malware from November 2018 through February 2021, stealing personal and banking information from victims to perpetrate financial theft. This malware also enabled further cyberattacks, including a ransomware assault on the University of Vermont Medical Center, which inflicted over $30 million in losses and critically hampered patient services.
U.S. Attorney Michael Easley and FBI Assistant Director Bryan Vorndran underscored the grave threats posed by malware like IcedID to the American economy, critical infrastructure, and national security. Penchukov’s prosecution underscores the FBI’s commitment to dismantling cybercriminal networks and the collaborative efforts of international law enforcement to uphold cybersecurity.