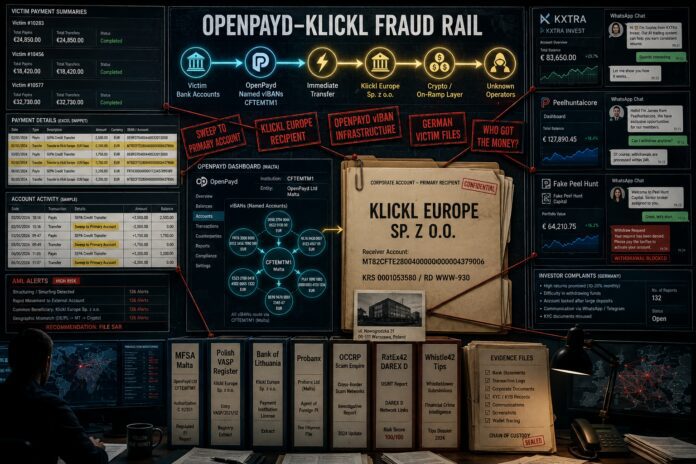
FinTelegram has reviewed a new batch of OpenPayd payment summaries gathered by victims of fake investment schemes. The pattern is brutal and consistent: victim deposits hit OpenPayd vIBANs and are immediately transferred to Klickl Europe Sp. z o.o. with the reference “Sweep to Primary Account.” In the readable files reviewed, hundred of thousands of Euros flowed through this OpenPayd–Klickl rail. This is no longer a single-victim case. It is a payment machine.
2-Minute Briefing
FinTelegram has reviewed a new batch of OpenPayd payment summaries received by victims after GDPR/DSAR requests. The documents show a repeated payment pattern: Payin from victim → immediate Transfer → Klickl Europe → “Sweep to Primary Account.”
FinTelegram analyzed the batch of victim payment files. The payment summaries show that each victim payment to OpenPayd was transferred to KLICKL EUROPE SP.z.o.o., BIC CFTEMTM1, receiver account MT82CFTE28004000000000004379006. This confirms the core FinTelegram finding: OpenPayd provided the vIBAN collection infrastructure; Klickl Europe received the swept victim funds.
OpenPayd’s own GDPR response to the victims confirmed the architecture. It states that OpenPayd provides services to corporate clients only, identifies Klickl Europe as the relevant client, explains that the IBAN was a named virtual IBAN linked to Klickl Europe’s payment account, and states that funds credited to that account became the property of Klickl Europe.
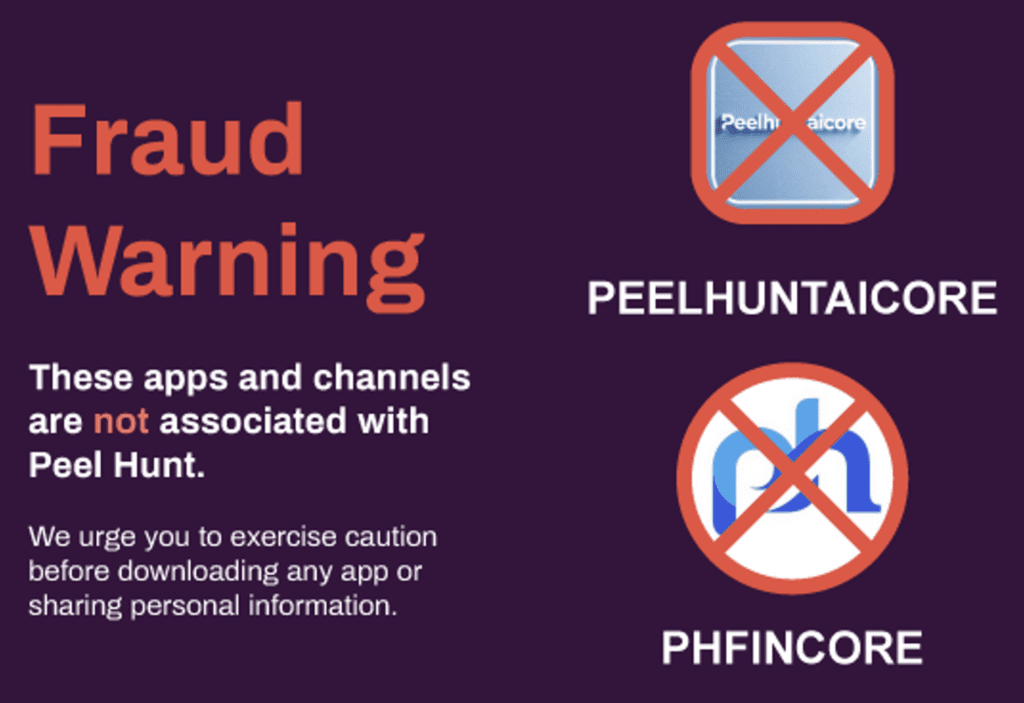
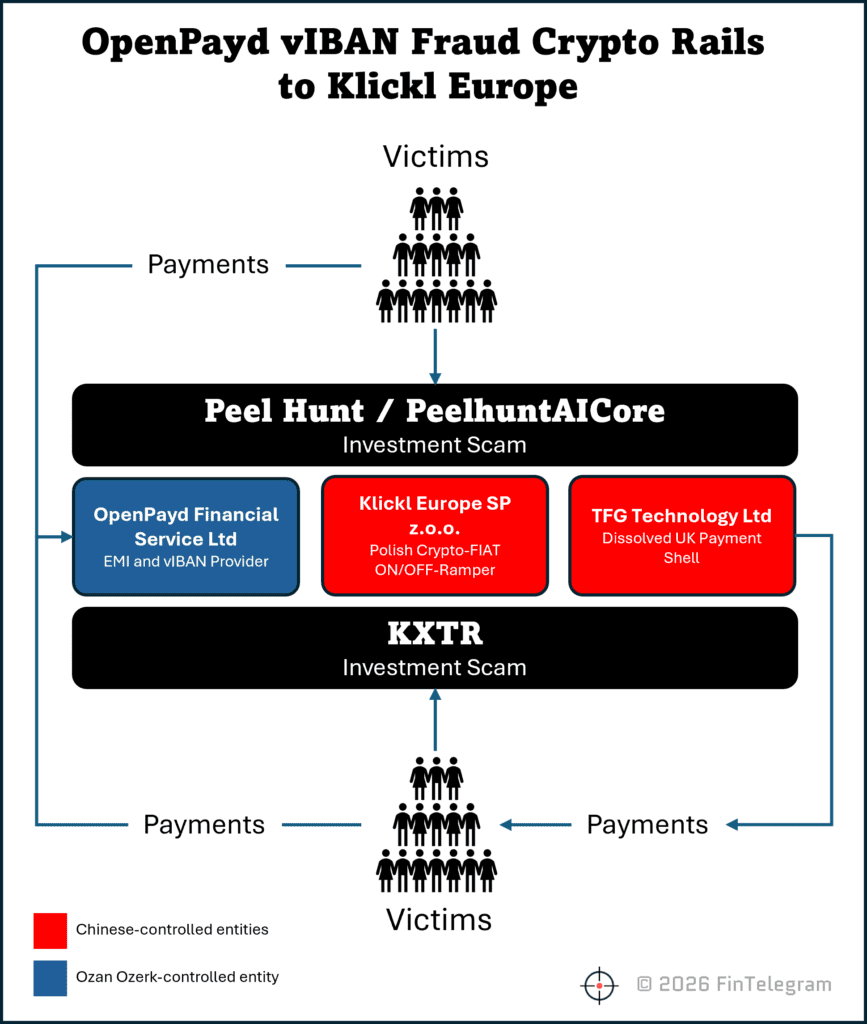
The new batch of victim files makes the case bigger. The pattern is no longer limited to KXTRA or one Peel Hunt / Peelhuntaicore victim. It points to a scalable fraud rail used against mainly German-speaking victims. The legitimate Peel Hunt has publicly warned that it does not use WhatsApp, downloadable apps or social media channels for regulated investment activity and says apps and WhatsApp channels using its name are not associated with the firm.
OCCRP’s Scam Empire reporting described how large investment-scam networks rely on payment providers and accounts to collect victim money. FinTelegram’s new OpenPayd/Klickl evidence fits that model.
Key Findings
- The new files show a systematic payment pattern.
Victim Payins into OpenPayd vIBANs were immediately matched by outgoing transfers to Klickl Europe with the reference “Sweep to Primary Account.” - The same Klickl account appears repeatedly.
The receiver account in the readable files is consistently MT82CFTE28004000000000004379006, BIC CFTEMTM1, receiver Klickl Europe Sp. z o.o. - The current verified batch already exceeds €665,000.
FinTelegram’s conservative review of readable Excel files plus two PDF summaries shows at least €665,733.74 in victim-fund flows through this rail. - The victims are predominantly German-speaking.
In the readable Excel files, sender accounts are mainly German IBANs, with additional Austrian accounts. This aligns with the Peel Hunt / Peelhuntaicore and KXTRA victim pattern. - OpenPayd’s GDPR response confirms the structure.
OpenPayd says the vIBANs are generated as reconciliation tools for corporate clients and that the relevant account belonged to Klickl Europe. It also says funds credited to that account became Klickl Europe’s property. - Klickl Europe is not a random payee.
Klickl discloses that Klickl Europe is incorporated in Poland under KRS 0001053580 and registered under Polish virtual-asset registration RD WWW-930 for exchange, brokerage and virtual-asset account activities. - This is a fraud-rail issue, not a paperwork issue.
If multiple scam frontends routed victims through OpenPayd vIBANs into Klickl Europe, regulators should treat this as a suspected payment-enabled investment-fraud network.
Read our OpenPayd reports here.
Key Data Table
| Entity / Mechanism | Role | Jurisdiction | Evidence | Red Flag |
|---|---|---|---|---|
| OpenPayd Financial Services Malta | vIBAN infrastructure / payment facilitator www.openpayd.com | Malta | GDPR response; payment summaries; BIC CFTEMTM1 | Victim deposits routed through OpenPayd infrastructure |
| Named OpenPayd vIBANs | Victim-facing deposit identifiers | Malta rail | OpenPayd says vIBANs are reconciliation tools linked to corporate clients | Creates personal-account appearance while funding corporate account |
| Klickl Europe Sp. z o.o. | Sweep recipient / corporate account holder | Poland | Repeated receiver in summaries; OpenPayd GDPR response | Central recipient of victim funds |
| Receiver account | Klickl Europe account | Malta IBAN rail | MT82CFTE28004000000000004379006 | Same account across multiple victims |
| Reference | Transfer logic | OpenPayd system | “Sweep to Primary Account” | Direct internal sweep pattern |
| Scam frontends | KXTRA, fake Peel Hunt / Peelhuntaicore, possibly more | Unknown operators | Victim files and Peel Hunt warning | Multiple brands, same suspected rail |
Rail Map
Victim bank account → OpenPayd named vIBAN → immediate transfer / “Sweep to Primary Account” → Klickl Europe corporate payment account → crypto/on-ramp or settlement layer → unknown scam operators
Known scam frontends so far:
- KXTRA / KKR Global Investment → OpenPayd vIBAN → Klickl Europe
- Fake Peel Hunt / Peelhuntaicore → OpenPayd vIBAN → Klickl Europe
Working hypothesis:
Additional fake investment brands → same OpenPayd/Klickl rail
FinTelegram Assessment
Established Facts
OpenPayd’s GDPR response confirms that the relevant vIBAN was linked to Klickl Europe’s payment account and that funds credited to it became Klickl Europe’s property. The Humer payment summary confirms Payins totaling €100,500 followed by transfers to Klickl Europe with the reference “Sweep to Primary Account.” The newly reviewed Excel summaries show the same pattern across multiple additional victims.
Strong Inferences
The evidence points to a structured victim-fund collection rail. OpenPayd provided the vIBAN infrastructure. Klickl Europe received the funds. The same receiver account and same sweep reference appear repeatedly. That is not random payment noise.
Working Hypotheses
Klickl Europe may have acted as an on-ramp or settlement layer for the operators behind KXTRA, Peelhuntaicore and related scam brands. A stronger hypothesis is that Klickl Europe may have been closer to the fraud operation than a passive processor. That remains to be proven.
Open Questions
Who was Klickl’s customer behind these flows? Were funds converted into crypto? Which wallets, exchanges or OTC desks received the money next? Did OpenPayd and Klickl file SARs/STRs? When did OpenPayd detect the pattern? Why was the rail not stopped earlier?
Whistleblower / Victim Call
FinTelegram is collecting: OpenPayd GDPR responses, OpenPayd “Summary of payments” Excel files, vIBANs, sender bank receipts, app screenshots, WhatsApp chats, fake Peel Hunt / Peelhuntaicore materials, KXTRA screenshots, wallet addresses, transaction hashes, Klickl responses, police reports, and regulator complaints.
Victims should send files directly via Whistle42. If one victim collects files for others, written consent should be obtained.