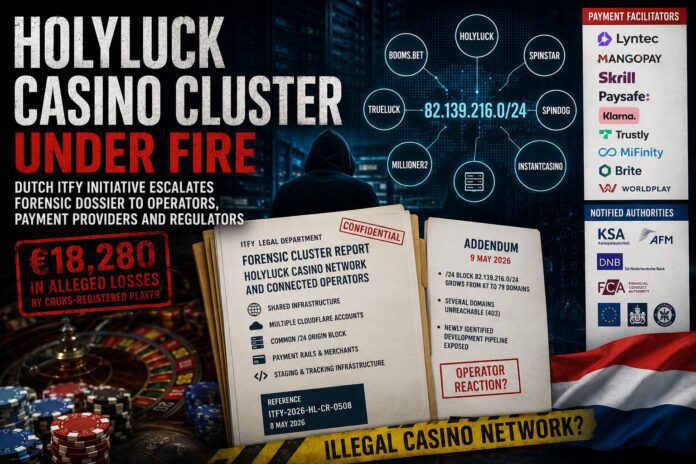
A Dutch legal-forensic initiative has pushed the illegal-casino debate into a new phase. ITFY Legal has served a detailed forensic cluster report, a Casino Monitor infrastructure report, and a follow-up addendum concerning the HolyLuck-linked casino network on casino operators, payment facilitators, regulators, government agencies and infrastructure providers. The reports draw on FinTelegram’s earlier investigative findings but go deeper into technical infrastructure analysis, mapping shared domains, Cloudflare accounts, origin IP blocks, payment descriptors and apparent staging environments.
Based on FinTelegram’s initial review, the ITFY findings align with and materially expand our own reporting on the HolyLuck / Booms.bet / Lyntec / SENDS payment-rail environment.
Key Findings
- Dutch initiative against illegal casino rails: ITFY Legal, based in the Netherlands, has prepared and circulated forensic reports concerning the HolyLuck Casino Network and connected operators.
- CRUKS player at the center: The reports concern a Dutch CRUKS-registered player who allegedly lost €18,280 across HolyLuck, Spinstar, Spindog, Millioner2 and InstantCasino.
- Cluster, not isolated casinos: ITFY alleges that the relevant casino brands form part of a broader operational cluster sharing infrastructure, legal operators, payment-presentation layers and mirror-domain architecture.
- FinTelegram findings confirmed and expanded: The ITFY report expressly cites FinTelegram’s earlier investigations into RevDuck, Sapphire Summit, Lyntec, SENDS/Smartflow and the HolyLuck payment rails, but adds a deeper forensic infrastructure layer.
- Payment providers and regulators on notice: The reports were circulated to casino operators, PSPs, regulators, public authorities, card/payment actors and infrastructure providers, including Cloudflare and Google-related channels.
- Post-service reaction: Within 24 hours after service of the first reports, ITFY observed changes in the cluster: several domains became unreachable, while the shared origin infrastructure allegedly remained stable and the observed domain footprint increased.
A Dutch Forensic Initiative Enters The Illegal Casino Battle
FinTelegram has received a set of reports and correspondence from ITFY Legal, a Dutch legal-forensic initiative, concerning what it calls the HolyLuck Casino Network and Connected Operators. The material was transmitted through the Whistle42 whistleblower channel and is directly relevant to FinTelegram’s ongoing investigations into illegal offshore casinos, merchant opacity and payment-rail abuse.
The first package consisted of a full forensic cluster report and a Casino Monitor infrastructure report. A one-page addendum followed one day later. According to the ITFY report, the matter concerns a Dutch resident registered in the Central Register for Self-Exclusion of Players (CRUKS), who was allegedly able to deposit funds with several unlicensed offshore casinos despite being barred from participating in remote gambling offers directed at Dutch residents. The report states an aggregate restitution position of €18,280.
This is not merely a private player complaint. It is a structured escalation package directed at casino operators, payment facilitators, supervisory authorities, public agencies and infrastructure providers.
The HolyLuck Cluster Allegation
The report identifies five principal casino operators in the client’s loss calculation: HolyLuck Casino, Spinstar Casino, Spindog Casino, Millioner2 Casino and InstantCasino.
It also links them to a wider network of brands including Booms.bet, TrueLuck, Kokobet, IgoBet, Winorio, Mega.bet, Bino, Fano, Moko, Starzino, Rakebit, Spinorhino, Casho-app, Luckygem, Baloo, Betory, Dragobet, Zazibet, Winhero and PlayMegaWin.
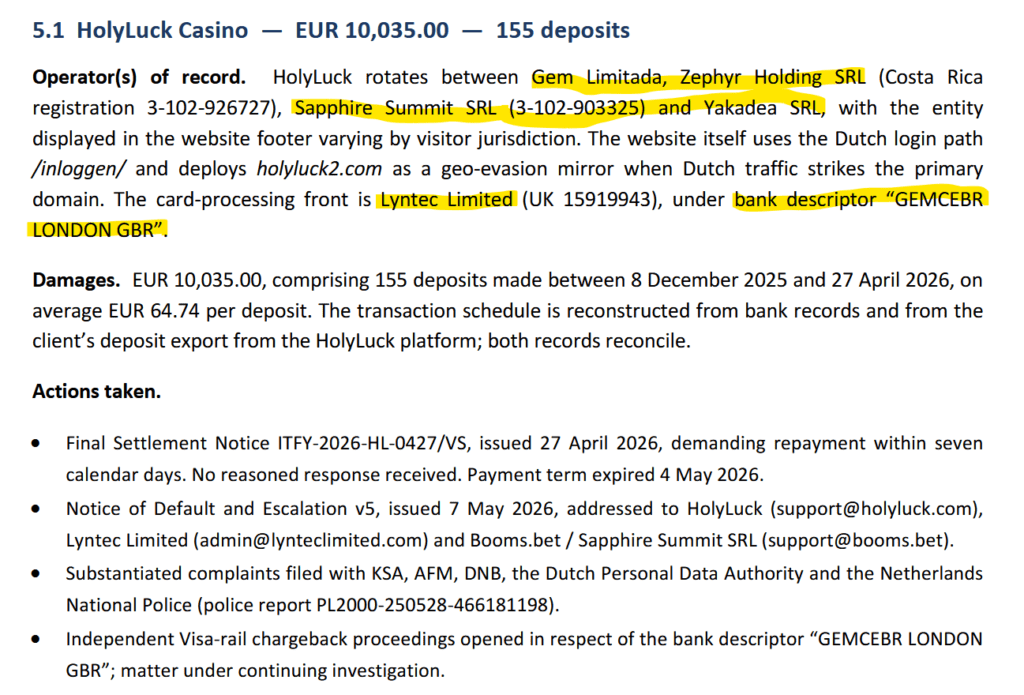
In a per-casino analysis, the ITFY report details, for each player, how the events unfolded and what actions the player took. See also the screenshot regarding the analysis of HolyLuck (right).
The core allegation of the report is simple but explosive: ITFY says the relevant casino brands should not be treated as independent operators, but as parts of a single operational cluster. This assessment aligns with that of FinTelegram regarding payment rails as well, where there are not only isolated payment facilitators but also networks of multi-layered payment rails that facilitate these illegal activities through these casino and domain networks.
The alleged losses of the player repretended by ITFY are broken down as follows:
| Operator | Alleged Deposits |
|---|---|
| HolyLuck Casino | €10,035 |
| Spinstar Casino | €2,855 |
| Spindog Casino | €1,805 |
| Millioner2 Casino | €1,780 |
| InstantCasino | €1,805 |
| Total | €18,280 |
The report states that the claims are based on bank-reconciled deposit records and player-account data.
From FinTelegram Reporting To Deeper Forensic Mapping

The ITFY report explicitly draws on FinTelegram’s earlier reporting. This is important. FinTelegram had already investigated elements of the HolyLuck / Booms.bet / RevDuck / Sapphire Summit / Lyntec / SENDS ecosystem, including the alleged use of UK-linked merchant fronts, payment descriptors and PSP routing layers.
ITFY takes that reporting and adds a deeper technical layer. The report states that its findings are supported by forensic infrastructure analysis, KSA sanction records, UK Companies House records, industry sister-site databases, operator disclosures and FinTelegram’s investigative series.
Based on FinTelegram’s initial review, the ITFY findings are broadly consistent with our own investigations and appear to build upon them. The ITFY material does not merely repeat prior allegations. It attempts to reconstruct the casino cluster technically — through domains, nameservers, origin IPs, MX records, TLS fingerprints, HTML hashes and payment-presentation layers.
That is where the report becomes particularly powerful.
The Methodology: Follow The Infrastructure
The Casino Monitor report describes a forensic clustering methodology based on public sources such as Certificate Transparency logs, urlscan.io, Wayback Machine records and manual additions. For each reachable domain, ITFY records infrastructure fingerprints including nameservers, IP addresses, /24 hosting blocks, MX records, SSL certificate hashes and HTML-body hashes. Domains sharing identical values are grouped as clusters.
The full ITFY report then identifies several key infrastructure signals:
- multiple Cloudflare nameserver pairs, allegedly indicating several separate Cloudflare accounts;
- convergence on the same origin infrastructure, especially the 82.139.216.0/24 block;
- shared or unusual MX configurations;
- HTML-template congruence at the payment-presentation layer;
- exposed developer or staging deployments;
- tracking and analytics domains linked to casino brands.
One of the most striking findings is the claimed use of multiple Cloudflare account-level compartments that nevertheless converge on the same origin block. ITFY interprets this as deliberate compartmentalisation: separate front-end exposure, shared underlying infrastructure.
The Casino Monitor report separately shows HolyLuck, TrueLuck, Booms.bet, Spinstar, Moko and other domains resolving into the same 82.139.216.0/24 environment.
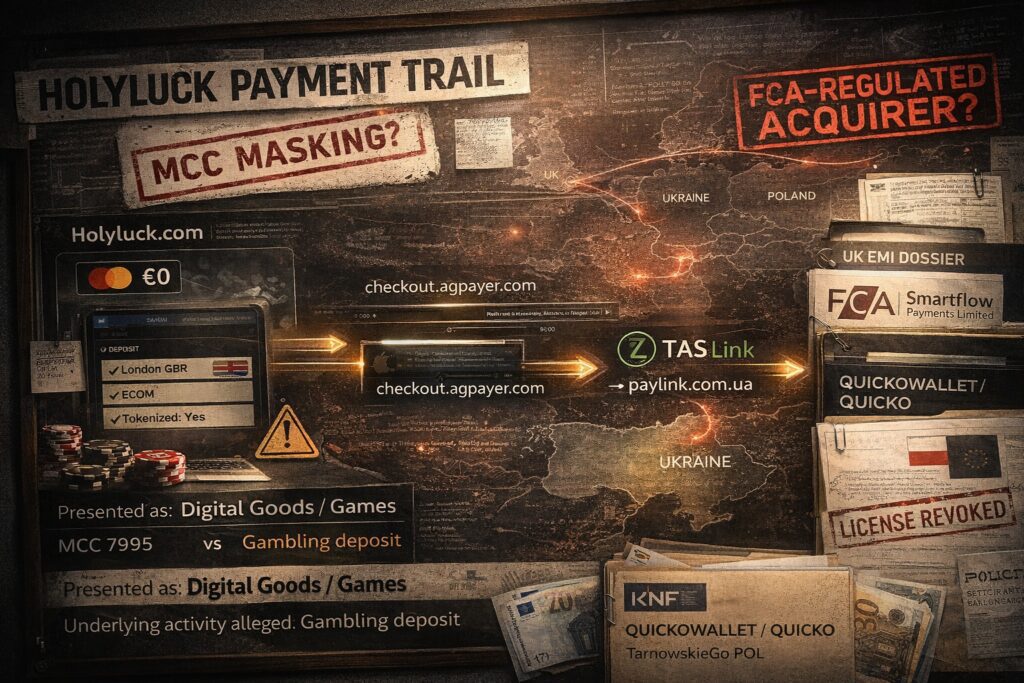
The Payment-Rail Dimension
The report is not limited to casino domains. It also targets payment rails and merchant presentation.
According to ITFY, the disputed flows involve or touch several payment actors and routes, including Visa, Klarna, Skrill/Paysafe, Mangopay, SaferSepa / AB Mano Bankas, MiFinity, Trustly/Brite, Worldpay, Mollie, and others. The report states that several payment-side investigations or disputes were opened and that some initial findings were favourable to the client.
The Lyntec / GEMCEBR element is especially relevant to FinTelegram. The report identifies Lyntec Limited as a UK-linked card-processing front associated with the descriptor “GEMCEBR LONDON GBR” and refers to the alleged use of MCC 5816 / Digital Goods instead of the gambling MCC 7995.
If confirmed, this would be classic transaction-laundering territory: gambling payments dressed up as digital-goods transactions.
The Addendum: Did The Cluster React?
The most dramatic element came one day later.
On 9 May 2026, ITFY circulated an addendum stating that material changes had been observed in the cluster within 24 hours after service of the original report. The addendum says the shared 82.139.216.0/24 origin block had increased from 67 domains to 79 domains, while several domains became unreachable, including instantcasino.com, millioner.com, millioner2.com, clickholyluck.com, clickwinorio.com, boomstrackers.com and trackingbino.bet.
ITYF interprets this as active operator-side rotation, not dissolution of the cluster. In other words: some front-end or tracking domains may disappear, but the infrastructure beneath them allegedly remains stable.
That is a key finding. Illegal casino networks are not static websites. They are adaptive conversion machines. Domains change. Mirrors appear. Trackers go dark. Payment fronts rotate. But the infrastructure pattern may survive.
The addendum also reports a newly identified development pipeline involving lottopark.work and whitelotto.work, with exposed subdomains such as admin, aff, api, casino, manager, mailhog and phpmyadmin, plus Polish DevOps terminology in path strings. ITFY describes this as operationally significant for Dutch and Polish authorities.
FinTelegram’s Initial Position
FinTelegram has not adopted every legal conclusion in the ITFY report. However, based on our initial review, the forensic material is serious, structured and highly relevant. It aligns with and expands upon several findings previously published by FinTelegram concerning HolyLuck, Booms.bet, Sapphire Summit, Lyntec, SENDS/Smartflow, RevDuck and related payment infrastructure.
The addendum is particularly important because it suggests that the report may already be producing operational consequences. If casino domains, trackers or staging endpoints move shortly after legal notice, regulators and PSPs should pay attention.
FinTelegram will continue reviewing the material and expects to publish follow-up reports on specific aspects of the ITFY dossier, including payment facilitators, merchant descriptors, Cloudflare and Google infrastructure, Dutch CRUKS implications, Polish-linked domains and the broader offshore casino ecosystem.
Call For Information
FinTelegram invites insiders, former employees, payment-service providers, acquiring banks, compliance officers, affected players and technical investigators to provide information about the HolyLuck Casino Network, Booms.bet, Spinstar, Spindog, Millioner2, InstantCasino, Lyntec Limited, SENDS/Smartflow, Mangopay, Skrill/Paysafe, Klarna, SaferSepa, Brite, Trustly, Cloudflare-hosted casino infrastructure, or related merchant descriptors.
Information can be submitted securely through the Whistle42 whistleblower platform.