The criminal case against former AirSoft CEO Shay Benhamou before the Bamberg Regional Court is not just another legacy binary-options story. It goes to the heart of a far bigger compliance question: when does a white-label software provider stop being a neutral technology vendor and become a knowing enabler of cyber-enabled investment fraud? German prosecutors appear determined to test exactly that boundary.
Key Findings
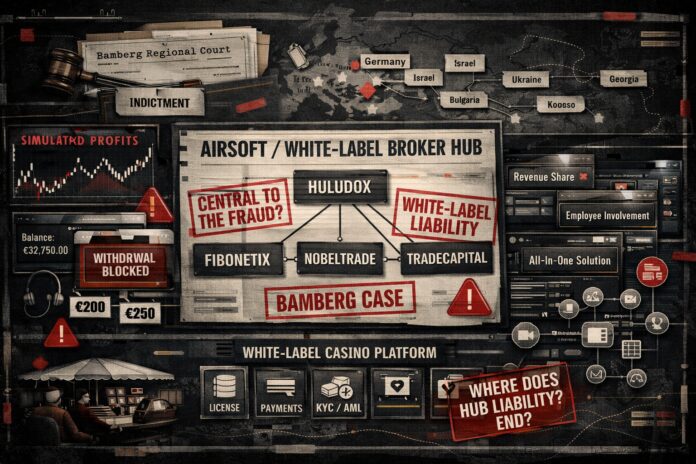
- German prosecutors have brought four counts of commercial and organized fraud against former AirSoft CEO Shay Benhamou in Bamberg, with alleged investor losses exceeding €94 million.
- OCCRP reports that prosecutors allege AirSoft’s brokerage software was “central to the fraud,” that the company shared in scam revenues, and that AirSoft employees were operationally involved in some cases.
- FinTelegram had already warned in its August 24, 2022 report that AirSoft was a venture of interest for German law enforcement and was repeatedly linked to scam-facilitating activities.
- The AirSoft case fits a broader enforcement pattern in which prosecutors increasingly target the technical infrastructure behind broker scams, not just the visible scam brands and boiler rooms.
- The same legal logic is relevant beyond broker fraud. In white-label casino and gaming structures, providers often control the licence umbrella, payment stack, and compliance framework, making “we only provide technology” an increasingly weak defense.
Report
A Case That Goes Beyond One Former CEO
The proceedings against former AirSoft CEO Shay Benhamou before the Bamberg Regional Court are significant because they target not merely a scam brand or a boiler-room operator, but the software layer behind fraudulent broker operations. According to OCCRP, opening arguments began on March 2, 2026, and the indictment covers Benhamou’s work as CEO of Israel-based AirSoft from March 2015 until at least the end of June 2021. Prosecutors accuse him of four counts of commercial and organized fraud and allege investor damage of more than €94 million.
This is what makes the case strategically important. It addresses a core question that has accompanied the binary-options and CFD fraud industry for years: can the provider of a white-label brokerage platform be held responsible when its software is used not for legitimate trading, but as the operational backbone of industrialized investor fraud?
FinTelegram Had Raised Red Flags In 2022
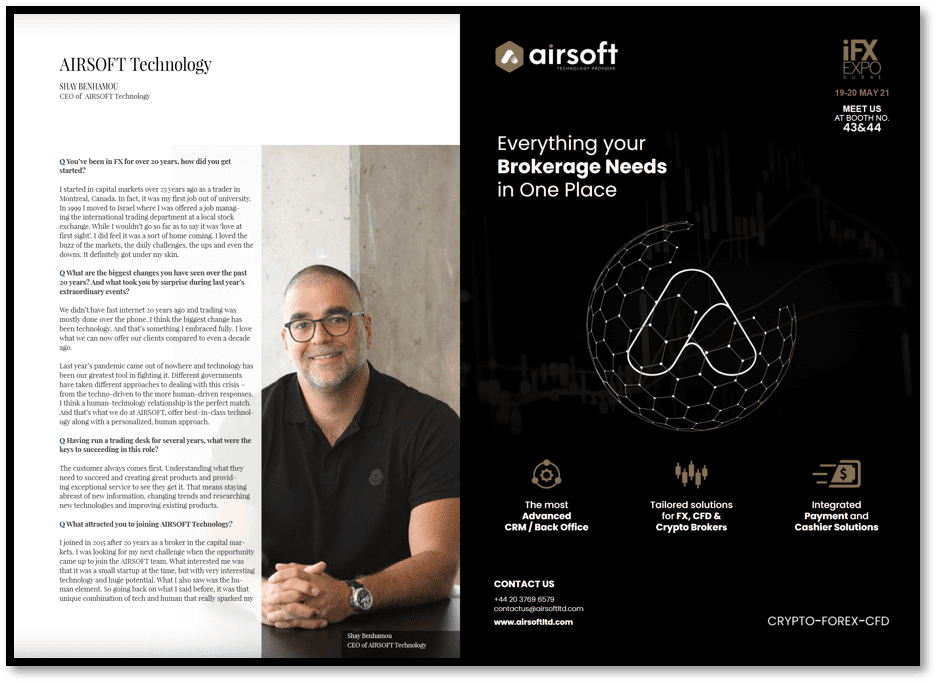
FinTelegram identified AirSoft as a high-risk white-label broker-platform provider long before the current German proceedings reached trial. In its August 24, 2022 report, FinTelegram described AirSoft as a venture of interest for German law enforcement because of alleged scam-facilitating activities. It also noted that the company repeatedly surfaced in connection with broker scams and identified Shay Benhamou as the company’s longtime CEO.
That early reporting now looks prescient. The present criminal case strongly suggests that German authorities did not view AirSoft as a peripheral vendor, but as part of the infrastructure that enabled multiple fraudulent broker operations to scale across jurisdictions. This tracks with what FinTelegram has argued for years: in cyber-enabled investment fraud, the visible broker brand is often only the storefront. The real continuity and control often sit deeper in the stack — with the software providers, CRM operators, payment facilitators, and other infrastructure enablers.
The Legal Fault Line: Neutral Vendor Or Knowing Enabler?
The defense position, as reported by OCCRP, is that the case raises a fundamental legal question about when a software provider may be held criminally liable for the misuse of its product by third parties. In abstract terms, that is a legitimate question. A generic technology provider cannot automatically be responsible for every illegal use of its product.
But the issue in AirSoft is not abstract. OCCRP reports that prosecutors allege Benhamou “knowingly and willingly” provided a brokerage “all-in-one solution” that was “central to the fraud” carried out by criminal groups in multiple countries. They also allege that AirSoft took a share of scam revenues and that, in some cases, AirSoft employees had to be operationally involved and in fact were involved.
That changes the legal picture materially. A provider ceases to look like a neutral software vendor when several indicators appear together: knowledge of criminal use, repeated servicing of obviously fraudulent operators, operational support, continuing access to the environment, customization of the platform, and direct participation in the revenues generated by the fraud. Once those elements are present, the software company begins to look less like a supplier and more like an infrastructure partner in the offense.
Why The Software Was Central To The Fraud
In broker scams, the software is not a passive technical accessory. It is the very interface through which deception is staged. The fake trading platform displays manipulated balances, simulated trades, artificial profits, and fabricated account histories that make the victim believe a legitimate investment process is taking place. Without that digital front end, the boiler-room pitch would lose much of its persuasive power.
According to OCCRP, the AirSoft software was allegedly used across multiple fraudulent brands, including Huludox, Fibonetix, Nobeltrade, Tradecapital, and Forbslab. Those brands were reportedly part of a wider network whose leaders were convicted by the Bamberg court in 2025 for scam operations run through call centers in countries including Bulgaria, Serbia, Ukraine, Georgia, Israel, and Kosovo.
That is why the software-provider question matters so much. If the platform was not merely sold once and forgotten, but remained embedded in the operational model of known scam brands, then liability analysis must look at the real function of the provider in the fraud chain. The law should assess substance over formal labels.
A Wider Enforcement Pattern Is Emerging
The AirSoft case is not isolated. It is part of a wider prosecutorial trend in which the infrastructure layer of online investment fraud is coming under direct criminal scrutiny. OCCRP notes that the Bamberg Regional Court had already heard another 2026 case involving software provider Mikheil Biniashvili and the Puma TS trading system. In that case, prosecutors said the software was deployed by hundreds of scam brands, and Biniashvili received a seven-and-a-half-year prison sentence in a plea deal after being found to have knowingly profited from fraudulent operations.
This is a major development. For years, enforcement focused primarily on boiler-room managers, visible broker brands, and front-facing fraud actors. Increasingly, however, prosecutors are moving upstream toward the technical layer that made these scams scalable: software providers, platform operators, and back-office enablers. The evolution of the German-led investigations supports that view. Eurojust said in 2023 that a coordinated action against a fraudulent online investment platform had already identified at least 33,000 victims and estimated losses of €89 million, with arrests and searches across Bulgaria, Romania, and Israel.
The message is clear: authorities are no longer satisfied with dismantling the visible fraud brands while leaving the infrastructure providers untouched.
The Tradologic Comparison Matters
The AirSoft proceedings also invite comparison with Tradologic, another major software provider in the broker-scam ecosystem. EFRI reports that on September 8, 2023, Tradologic co-owner Ilan Tzorya. received an eight-year prison sentence and former CEO Micha Golod received six years, while noting that both verdicts are under appeal and therefore not yet final.
Even though those judgments are not final, they underline an important point: European prosecutors and courts are increasingly prepared to examine whether the provider of the software environment for fraudulent broker schemes was knowingly embedded in the criminal model. The legal theory is not radical. It reflects the practical reality of how cyber-enabled investment fraud worked for years: the software was not neutral infrastructure floating in a vacuum; it was often the organized, monetized backbone of the deception.
Insider Evidence And Whistleblower Material Are Crucial
FinTelegram has for years received insider and whistleblower information suggesting that major broker-platform providers such as AirSoft, PandaTS, Puma TS, and Tradologic were not blind to the nature of many of their clients. On the contrary, the information received indicates that these providers often had detailed visibility into their clients’ operations and in some cases supported them with additional services, including payment integrations and technical support that went beyond ordinary software licensing.
This aspect is especially important from a legal standpoint. Knowledge is rarely proven by one email or one public statement. It is often inferred from patterns: repeated servicing of notorious scam brands, continuous back-office support, privileged technical access, revenue participation, and the absence of any meaningful compliance off-ramp despite obvious red flags. The more integrated the provider is into the client’s operations, the harder it becomes to sustain a plausible-deniability defense. That is precisely why insider evidence can become decisive in cases like Bamberg.
The Relevance Beyond Binary Options: White-Label Casino And Gaming Hubs
The implications of the AirSoft case go beyond the legacy broker-fraud sector. The same structural issues arise in white-label online gambling and casino models. SOFTSWISS itself explains that in a white-label structure, the operator launches the brand under the provider’s existing licence and integrated platform, while “the legal accountability lies with the licence holder – the platform provider.” It also states that white-label systems typically include integrated payment methods, KYC/AML tools, CRM features, technical maintenance, hosting, and compliance monitoring.
That matters because it shows how deeply the platform provider sits inside the operational model. A provider that supplies the licence umbrella, payment stack, compliance framework, and core backend cannot easily present itself as a detached software vendor. Its entire value proposition is built on integration and control. SOFTSWISS also notes that local licensing regimes in markets such as Germany, the UK, Sweden, and the Netherlands do not permit this kind of white-label arrangement, and that the provider’s licence defines where the platform may and may not operate.
This is where the comparison with illegal or unlicensed gambling becomes legally relevant. If a white-label gaming hub knowingly provides its infrastructure to operators targeting restricted jurisdictions, processes payments through centralized stacks, and remains responsible for compliance monitoring under its licence umbrella, then the old formula — “we are only the technology provider” — becomes increasingly untenable. The front end may be different from a broker scam, but the liability logic is strikingly similar: knowledge, control, operational involvement, and economic participation.
Where Hub Liability Should Begin
The real question raised by the AirSoft case is not whether software developers should be criminalized for building technology. They should not. The real question is where legal responsibility begins when a provider knowingly services fraudulent or unlawful operators through an integrated white-label hub.
In practical compliance terms, that boundary should be examined through a number of indicators: whether the provider knew or must have known of the unlawful business model; whether it continued servicing the client despite obvious red flags; whether it retained privileged operational access; whether it integrated or controlled payments, CRM tools, and other mission-critical systems; and whether it shared in the revenues generated by the unlawful conduct.
Where those indicators are present, responsibility does not end with the licensing agreement or software contract. At that point, the provider becomes part of the enabling infrastructure. That is why the Bamberg proceedings deserve close attention well beyond the legacy binary-options field.
Conclusion
The Shay Benhamou case may become a landmark in the legal treatment of cybercrime infrastructure. It tests whether those who built, operated, and profited from the platforms behind fraudulent broker brands can still hide behind the claim that they merely supplied neutral technology. German prosecutors appear to be arguing that AirSoft crossed that line. If the court agrees, the implications will extend far beyond AirSoft — to PandaTS, Puma TS, Tradologic, and to white-label hub models in adjacent sectors such as online gambling.
For FinTelegram readers, the lesson is straightforward: the visible scam brand is often only the surface. The real leverage points sit deeper in the stack — in the software providers, payment hubs, and compliance umbrellas that make fraud and illegal cross-border operations scalable. The age of plausible deniability for these infrastructure operators may be coming to an end.
Call for Whistleblowers
FinTelegram continues to investigate the software, payment, and white-label infrastructure behind broker scams and illegal gambling operations. If you have information about AirSoft, Shay Benhamou, PandaTS, Puma TS, Tradologic, white-label casino hubs, integrated payment stacks, or licence-umbrella structures used for unlawful cross-border operations, share it securely through Whistle42.