The U.S. Justice Department (DOJ) announced the seizure of internet domains involved in selling the Warzone RAT malware, a tool cybercriminals use to infiltrate and pilfer data from unsuspecting victims’ computers covertly. This operation also saw the unsealing of indictments against individuals based in Malta and Nigeria, respectively, for their roles in disseminating the malware and aiding cybercriminals.
The seized domains, including www.warzone.ws, were known for retailing the Warzone RAT malware, a sophisticated remote access trojan that allowed cybercriminals to access victims’ computers stealthily. This malware enabled a range of illicit activities, such as file system browsing, screenshot capturing, keystroke recording, and even spying on victims through their webcams without their knowledge or consent.
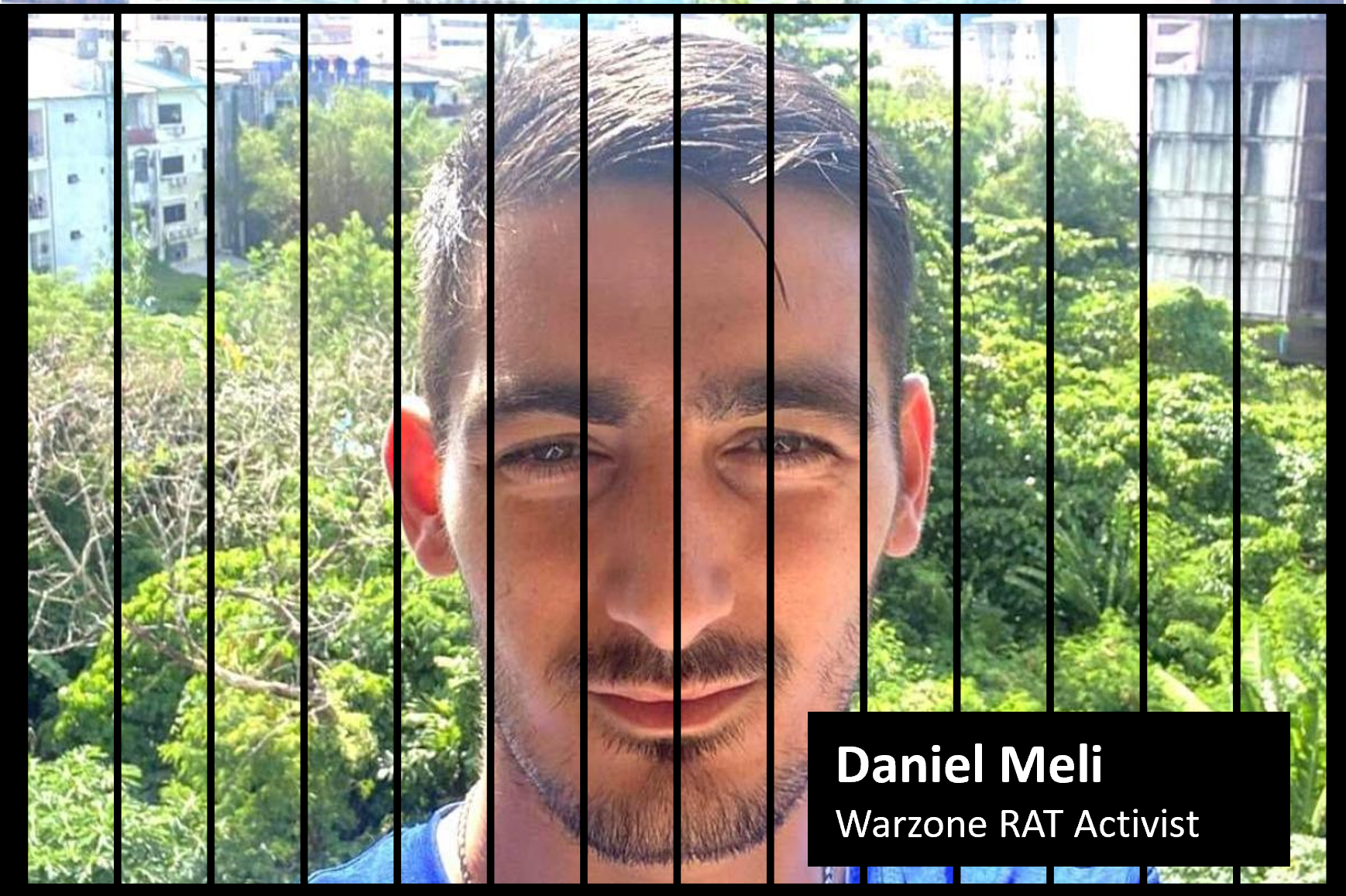
The law enforcement actions resulted in indictments against Daniel Meli, 27, of Malta and Prince Onyeoziri Odinakachi, 31, of Nigeria. Meli was apprehended in Malta on February 7 following a request from the United States seeking his extradition. Charged with multiple offenses, including unauthorized computer damage and the illegal sale of electronic interception devices, Meli has been accused of offering malware products and services to cybercriminals since at least 2012. Odinakachi was arrested in Nigeria on the same day, facing charges for his involvement in supporting users of the Warzone RAT.
Meli consented to the extradition and is being kept at the Corradino Correctional Facility in Malta in the meantime. His lawyer, Joe Giglio, invoked the rule of specialty, meaning that he was to be extradited to answer only for the charges indicated in the relative documentation.
This crackdown on the Warzone RAT infrastructure is part of a broader initiative to dismantle the digital tools leveraged by cybercriminals. The operation was spearheaded by the FBI, with assistance from international partners, including Europol and law enforcement agencies in Canada, Croatia, Finland, Germany, the Netherlands, and Romania.
The charges of conspiracy, obtaining authorized access to protected computers to obtain information, illegally selling an interception device, and illegally advertising an interception device each provide for a sentence of up to five years in prison, three years of supervised release, and a fine of $250,000, or twice the gross gain or loss, whichever is greater. The charge of causing unauthorized damage to protected computers provides for a sentence of up to 10 years in prison, three years of supervised release, and a fine of $250,000, or twice the gross gain or loss, whichever is greater.